Introduction
Last year, we published two pieces on digital supply chains and geopolitics. We made predictions. We promised to follow up. It's been almost a year. This piece will cap off the trilogy and provide an up-to-date look at last summer’s ideas.
Cloud Provider Diversification
During our coverage of supply chain shocks, we took a position that shifting geopolitical postures would drive geographic cloud diversification. Our initial follow-up found:
Peak diversification occurred in 2022, not in response to 2025 supply chain shocks.
Chinese providers (the most logical geopolitical hedge) have been flat at 7% for three years.
European alternatives hold a minimal 2% combined market share.
Internal US competition dominates, not geographic diversification.
This meant our thesis was….wrong. Almost a year later, we need an update. Here are the figures:
US Providers had 67-68% market share in 2025 (details below):
Amazon AWS: 30% in Q2, 29% in Q3, and down to 28% in Q4
Microsoft Azure: 20% in Q2 & Q3, 21% in Q4
Google Cloud: 13% in Q2 & Q3, then 14% in Q4
Oracle OCI: 3% in Q2, Q3, and (surprise, surprise), 3% in Q4
IBM Cloud: 2% (flat)
Smaller players, including Akamai, CoreWeave, Databricks, OpenAI, and Snowflake, at <=1%.
In the last two quarters of 2025, non-US providers had 12% market share (broken down below):
Chinese providers total 10%: Alibaba Cloud (flat at 4%), Tencent Cloud (flat at 2%), Huawei (flat 2%), Baidu (1%), China Telecom (1%), China Unicom (1%).
European providers: IONOS Cloud (1%), SAP Business Data Cloud (1%) = 2% total
Japanese providers: NTT (1%), Fujitsu (1%) = 2% total
Localized numbers paint a consistent picture. The European cloud provider market share decreased from 29% in 2017 to 15% in 2022. Since then, it has stayed around 15%. Even within Europe, the big 3 names are Amazon, Microsoft, and Google, and they account for 70% of the market.
After that, SAP and Deutsche Telekom lead the European market, each accounting for 2%.
Then, the long tail consists of OVHcloud, Telecom Italia, Orange, and niche regional players.
The significant trend outside the continued market share redistribution within US providers is a broader spectrum of smaller “neo-clouds” staking claims at the margins, domestically and internationally :
Winners: The highest growth rates among tier two cloud providers are CoreWeave, OpenAI, Oracle, Databricks, and Huawei.
Losers: In Q3, AWS lost a step with Azure losing a couple points, with Google Cloud and smaller players nipping at their heels. Oracle staying flat at 3% is interesting given their rapid share price growth and deals.
Non-US providers show some life, with Huawei growing fast and a broader list of Chinese providers. While the top numbers show US dominance, the fragmentation and wider breadth of names hint at a world where our thesis proves correct.
Verdict: The numbers say we're still wrong. US providers dominate. Non-US market share is flat. Internal US competition (Google and Oracle gaining on AWS and Azure) is the dominant dynamic, not geographic rotation. But the rest of this piece tells a different story. The market share hasn't moved, but the risk calculus is shifting underneath it.
Sources: CRN Q4 2025 Cloud Market Share, Synergy Research Group
Dependency Management as a Core Business Function
Alongside cloud diversification, another major prediction from the last piece is the increasing relevance of digital risk management as a core business function. If the market share data above shows our geographic thesis struggling, this is where the qualitative evidence runs in our favor. Organizations are learning (painfully) that their digital supply chains are as fragile as their physical ones.
Here are the incidents and market movements that provide updated case studies in this trend:
AWS Goes Down (Again)
In late November 2025, a major AWS outage affected thousands of companies and gave folks across all job functions an unexpected day off. The post-mortem showed that DNS records in DynamoDB were disrupted when an automation managing these records suffered a latent race condition, creating an incorrect empty DNS record for the service's regional endpoint. This cascaded into crashed major consumer apps and business systems worldwide because their EC2 servers and network load balancers relied on DynamoDB processes.
Here's the kicker: the entries in Amazon's database services that map domains tried to write to the same spots, creating an empty entry. This affected so many people because these services ran on us-east-1 (the most popular region in the world for cloud deployments, aka the default region AWS offers when you first spin up one of these resources). Outside of all the technical work that AWS did related to recovery, the most bitter pill to swallow is that if someone had simply picked a different option than the default deployment, they could have been spared hours of downtime, lost revenue, and pissed off users.
Cloudflare Takes Down Half the Internet
In the same month, there was a worldwide outage due to Cloudflare being down. For those a little bit new to the scene: Cloudflare is a core service in the infrastructure of companies worldwide. When their network goes down, so does a significant chunk of the internet. Funnily enough, the issue also came from a database. A database system's permission level changed, which cascaded into more data being added to a file than usual. This may not seem like much, but this particular file was a "feature file" that machine learning models read. Specifically, the foundation of Cloudflare's Bot Management system. The file doubled in size and was then pushed to all of Cloudflare's global network machines. The software on these machines has a features hard limit for performance reasons, so when the bloated file arrived, the system panicked and crashed. This had several downstream effects on other aspects of Cloudflare's infrastructure and platforms like Twitter, ChatGPT, Spotify, Canva, and thousands of other services went dark.
Source: Cloudflare Post-Mortem
The Hits Keep Coming
A major Microsoft outage brought down Microsoft365 (which needs no introduction). Then, in January 2026, there was another Cloudflare outage AND another AWS outage. The industry isn't getting more resilient; it's getting more dependent on fewer chokepoints.
Verdict: Our prediction that technical dependencies can no longer remain strictly within engineering's domain is looking increasingly correct. These aren't obscure technical incidents. They're business continuity events that hit earnings calls and board meetings.
Sovereign Tech: From Buzzword to Budget Line
If the outages show the operational risk, the policy moves show the strategic response. Organizations of all scales are countering the changing world trade dynamics and establishing "sovereign tech." This section is where we see the most concrete movement (not in market share, but in institutional posture).
The International Criminal Court Ditches Microsoft
The International Criminal Court is replacing Microsoft software with an open-source alternative, Open Desk, which offers a version of the common suite of Office365 and Google Workspace products like file and document management, calendars, task tracking, etc. The marketing uses the tag line: "Level up to a truly sovereign workplace." Emphasis mine, but would you look at that?
Source: Yahoo Tech
France Boots Zoom
The French government decided to move away from Zoom to a home-grown French alternative, Visio. A French official said their aim was to "guarantee the security and confidentiality of public electronic communications by relying on a powerful and sovereign tool."
Source: Gizmodo
Building European: Harder Than It Looks
Of course, making changes is easier said than done, as noted last year. Robert, a European based founder wrote a sharp and honest analysis on building their startup on an entirely European stack. Some names are familiar (Hetzner is one we've taken a look at before at Sitebolts), while others are new. This piece is excellent because it highlights the cons, not just the pros. Some of those cons include leaving GitHub, email and domain pricing, and the fact that the top AI frontier labs remain American (such as Anthropic, who we'll discuss below).
Source: Made in EU - It Was Harder Than I Thought
CISPE vs. The EU Cloud Sovereignty Framework
Meanwhile, top European cloud players are clashing with the sovereign cloud initiatives we've covered in the past. The folks over at the "CISPE" (Cloud Infrastructure Service Providers in Europe) spoke out against the EU Cloud Sovereignty Framework, which according to them, will "likely lead to no changes in the market."
Source: Yahoo News
AWS Responds: The European Sovereign Cloud
Of course, the American hyperscalers aren't going to sit around and watch this happen. They are taking these potential shifts more seriously than previous attempts at similar moves, using the newest sovereign tech language for their own cause. In January 2026, AWS launched its European Sovereign Cloud: a new, independent cloud for Europe that is "physically and logically separate" from other AWS Regions. They've created a new parent company under German law, appointed EU citizens as managing directors, and established an advisory board comprised exclusively of EU citizens. Amazon is investing €7.8B in this infrastructure.
This could be read two ways. One: geographic sovereignty is becoming material enough that AWS feels compelled to build entirely separate infrastructure. Two: US hyperscalers will simply absorb the sovereignty demand without ceding market share. The honest answer is probably both.
Source: CNBC, AWS Announcement
Verdict: Mixed signals. Some point toward our thesis (ICC, France, AWS's €7.8B bet on European sovereignty). Some point against it (CISPE's complaint, the founder's blog post showing how hard it is to go European-only). We're not calling this one definitively. The market share numbers say we're wrong, but the institutional posture shifts say the question isn't closed.
The New Attack Surface: AI Labs and Data Centers
And finally, the developments that connect our digital supply chain thesis to actual geopolitical conflict. This is the section we didn't anticipate writing last spring.
Claude, Palantir, and the DOD
Here’s an odd one: the ongoing struggle between Anthropic (a leading frontier lab for state of the art AI) and the Department of Defense (uh I imagine we are all familiar with them). The Department of Defense uses Palantir software (not going to bother going down that rabbit hole), which runs Anthropic models under the hood. The short version: Anthropic partnered with Palantir in late 2024 to provide Claude on classified networks. In July 2025, Anthropic signed a $200 million contract with the DOD, with terms stipulating certain limits via its "acceptable use policy" (including prohibitions on mass domestic surveillance and fully autonomous weapons).
Then things escalated. Reports emerged that Claude was used during the operation to capture Venezuelan President Nicolás Maduro via Palantir's Maven intelligence analysis program. Anthropic investigated and found no violations of its usage policies, but the DOD pushed back on Anthropic's posture of investigation. Defense Secretary Pete Hegseth issued a memorandum in January 2026 stating that AI models incorporating "ideological tuning" have no place in the "Department of War."
On February 26th, Anthropic CEO Dario Amodei announced: "we cannot in good conscience accede to their request." The company wanted assurances that Claude would not be used for fully autonomous weapons or mass domestic surveillance of Americans. The DOD wanted "any lawful use" without additional restrictions.
The outcome: President Trump ordered federal agencies to stop using Anthropic. Secretary Hegseth declared any contractor doing business with the US military is barred from commercial activity with Anthropic. And in an unprecedented move, the administration designated Anthropic (an American company) a "supply chain risk."
This is a first. An American AI company labeled a supply chain risk by its own government. The implications for the broader ecosystem are significant: defense contractors are now scrambling to replace Claude, and the locus of dispute isn't technical reliability. It's who gets to define acceptable use of frontier AI.
Sources: NBC News, CNBC, Breaking Defense, Nextgov
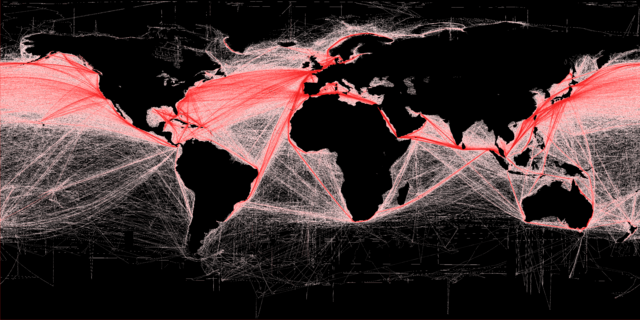
Drones Hit AWS Data Centers
Somewhat relatedly, the latest attack vectors in the Middle East conflict are data centers and server farms operated by American hyperscalers. In early March 2026, Iranian drone strikes damaged three AWS facilities in the Gulf region: two in the United Arab Emirates and one in Bahrain. This is believed to be the first time data centers have been deliberately targeted for military strikes in a conflict.
Iran's IRGC stated that the Bahrain facility was specifically selected "to identify the role of these centers in supporting the enemy's military and intelligence activities." AWS confirmed structural damage, disrupted power delivery, and water damage from fire suppression systems. Core services (EC2, S3, DynamoDB, Lambda, RDS) reported elevated error rates across the Gulf. Emirates NBD, Careem, and payment companies like Alaan reported outages.
The boundary between commercial cloud computing and military operations has largely vanished. The Pentagon's Joint Warfighting Cloud Capability runs on the same commercial infrastructure that serves banks and ride-hailing apps. Claude itself runs on AWS. When commercial data centers host military workloads, they become military targets.
As one analyst noted to Fortune: "If data centers become critical hubs for transiting military information, we can expect them to be increasingly targeted by both cyber and physical attacks."
Sources: DefenseScoop, Fortune, CNBC, Rest of World
Verdict: The Anthropic/DOD dispute and the AWS data center strikes are two faces of the same transformation. Digital infrastructure is no longer civilian-by-default. The question of where your workloads run, and who controls the models they depend on, has become a question of strategic posture, not just technical architecture.
Conclusion
When we posted our take on the digital supply chain last spring, we certainly didn't expect to revisit it under these circumstances. We thought we'd be tracking market share shifts and enterprise procurement patterns. Instead, we're watching drone strikes on data centers and AI companies getting labeled national security threats by their own government.
Here's where we stand after a year:
Geographic diversification thesis: Still wrong on the numbers. US providers dominate. Non-US market share is flat. Internal US competition (Google and Oracle gaining on AWS and Azure) is the dominant dynamic, not geographic rotation.
Dependency management thesis: Increasingly correct. The AWS, Cloudflare, and Microsoft outages are business continuity events now, not just IT incidents. Boards are paying attention. Insurance underwriters are repricing risk.
Sovereign tech thesis: Jury's still out. The institutional moves (ICC, France, AWS's European Sovereign Cloud) suggest the idea has traction. But market share hasn't followed. The European founder's experience shows how hard it is to go fully non-US. And CISPE's complaint suggests even European cloud providers are skeptical about EU sovereignty frameworks.
The new front: This is the development we didn't anticipate. Anthropic being labeled a supply chain risk by its own government. AWS data centers taking drone strikes. The line between commercial and military infrastructure has effectively dissolved. This changes the risk calculus for everyone with workloads in contested regions, or running on models whose acceptable use policies conflict with state interests.
No one ever got fired for buying IBM. No one ever got fired for deploying on AWS in us-east-1. But increasingly, no one is getting promoted for it either. As global systems and infrastructure rails get battered by the changing macro conditions, the safe default is becoming the risky assumption. Whether that translates into actual market share rotation remains to be seen. The conditions for it have never been more favorable.